- Shadow IT in government refers to unauthorized software, apps, and communication tools used outside of official IT oversight.
- Government agencies are among the highest-risk environments for shadow IT, given the sensitivity of the data handled and the regulatory frameworks that govern it.
- The most common driver is friction: when approved tools fail to meet operational needs, staff find alternatives on their own.
- Unmanaged shadow IT creates data sovereignty gaps, compliance failures, and attack vectors that adversaries can exploit.
- Managing shadow IT requires both policy enforcement and deploying tools that employees will actually use.
- Sovereign, self-hosted communication platforms eliminate the need for unauthorized workarounds.
The core problem: shadow IT in government is already inside your perimeter
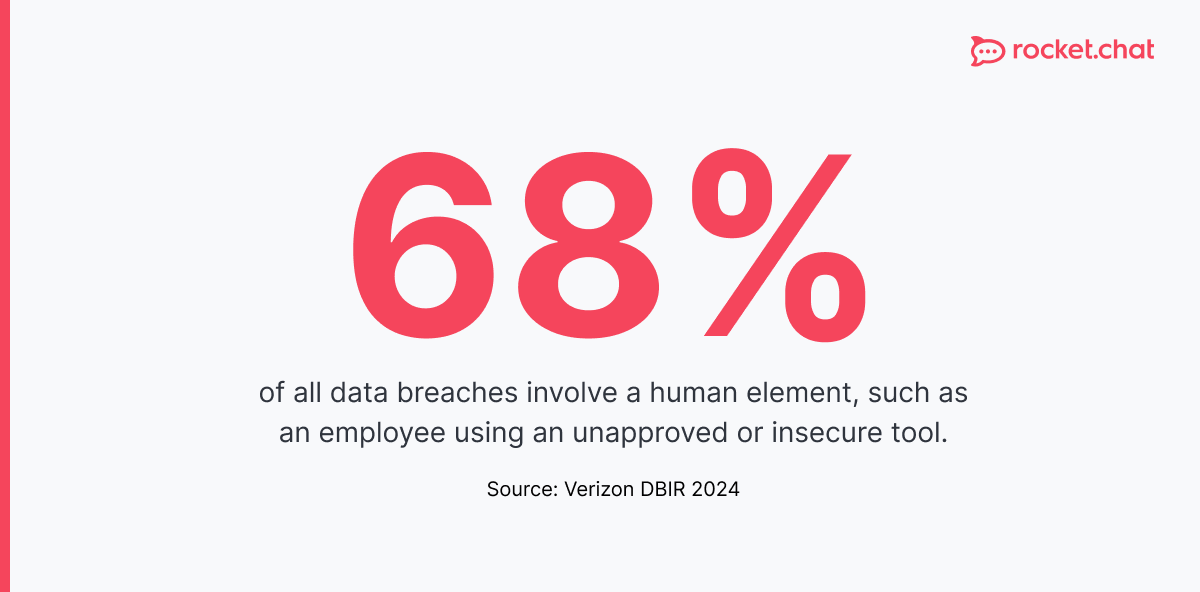
Shadow IT in government is not a fringe risk — it is a systemic one. A NinjaOne survey of 400 public sector managers across the US, Europe, and Oceania found that 49% of public sector employees rely on unauthorized software to complete their work, with 52% actively bypassing security policies. Gartner estimates that shadow IT accounts for 30 to 40 percent of IT spending in large enterprises, with Everest Group putting the figure at 50 percent or more. Government is not immune to either dynamic.
The defining characteristic of shadow IT is invisibility. When a civil servant sends a classified briefing over a consumer messaging app, or a defense contractor shares documents through a personal cloud storage account, the event is rarely flagged. There is no audit trail. There is no incident report. The data simply moves beyond the boundary of institutional control.
The consequences are not hypothetical. The 2022 investigation into UK government officials using WhatsApp for sensitive communications during the COVID-19 pandemic revealed systemic gaps in public records compliance and data governance. In the United States, the use of personal email for government business has triggered formal investigations at the federal level on multiple occasions.
Shadow IT in government is a structural failure, not a behavioral one. When institutional tools are slow, siloed, or inadequate, employees do not stop communicating — they route around the obstacle.
Why shadow IT takes hold in government environments
Government IT procurement is slow by design. Security reviews, procurement cycles, and interoperability requirements create timelines measured in years, not months. Operational needs move faster. When a joint task force needs a shared workspace in 48 hours, approved channels frequently cannot deliver.
The result is a predictable pattern. Teams under operational pressure adopt consumer tools — WhatsApp, Telegram, Signal, Slack, or Google Workspace — because they work immediately. Over time, these tools become embedded in workflows. By the time institutional IT becomes aware, the dependency is structural.
Several compounding factors accelerate this dynamic:
- Remote and hybrid work expanded the attack surface by pushing collaboration outside secure facilities.
- Coalition and inter-agency operations create demand for shared communication tools that cross organizational boundaries, where no single approved platform dominates.
- Generational shifts in the workforce bring personnel who default to consumer applications and experience friction with legacy government systems.
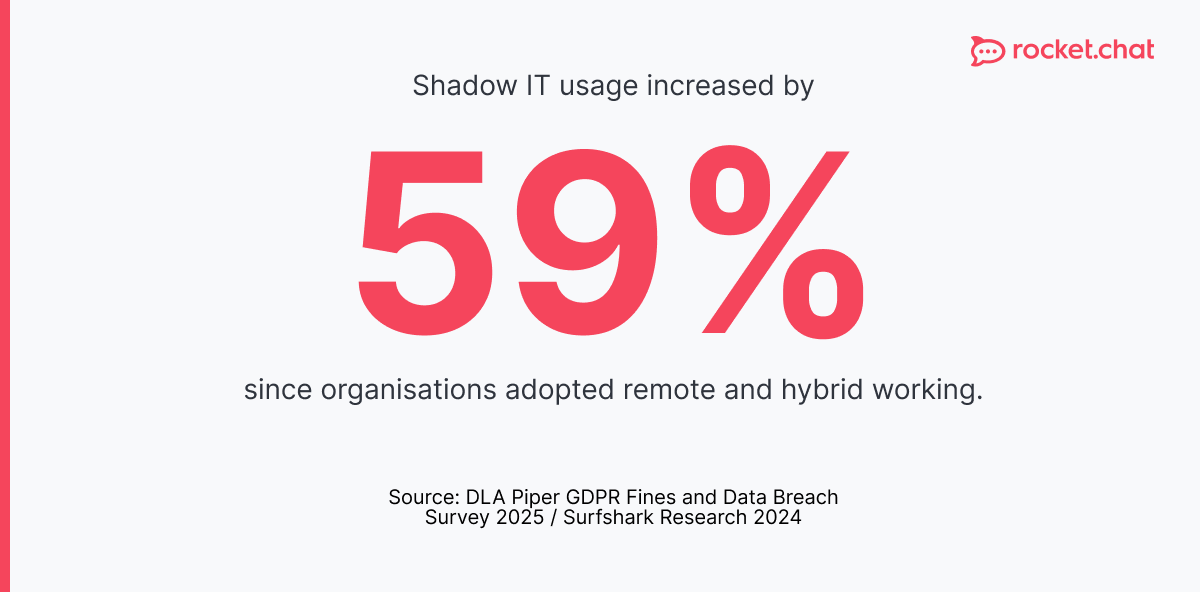
The most commonly adopted shadow IT categories in government are messaging and collaboration tools, file sharing platforms, and video conferencing applications — precisely the tools that are central to daily operations.
Shadow IT risks in government: what is actually at stake
The risks of shadow IT in government are not theoretical. They cluster into three categories: data sovereignty, compliance, and operational security.
Data sovereignty and jurisdictional exposure
When government staff use consumer cloud platforms, data is processed and stored under the terms of service and jurisdictional laws that govern those platforms — not under national or institutional policy. A message sent through a US-headquartered consumer app may be subject to US legal process regardless of where the sender or recipient is located.
This is not a hypothetical edge case. The EU's General Data Protection Regulation (GDPR) and the US CLOUD Act create directly conflicting obligations for organizations that use US-based cloud services to process European data. For European government agencies, this represents a structural compliance risk that shadow IT amplifies significantly. Understanding GDPR-compliant messaging practices is a prerequisite for any government communications policy.
Understanding GDPR-compliant messaging practices is a prerequisite for any government communications policy in Europe.
Regulatory and records compliance
Most government jurisdictions impose legal requirements on records retention, data classification, and communications archiving. Shadow IT tools typically lack the administrative controls needed to satisfy these requirements. Data sent through an unauthorized platform cannot be systematically archived, audited, or produced in response to freedom-of-information requests.
The NIS2 Directive in Europe imposes binding cybersecurity obligations on essential services and digital infrastructure operators, including government entities. Organizations that cannot demonstrate control over their communications environment face material compliance exposure. NIS2 compliance requires, at minimum, full visibility into where sensitive communications occur.
Attack surface expansion
Every unauthorized tool represents an additional credential set, an additional network endpoint, and an additional data store that the institution's security team cannot monitor, patch, or respond to. Adversaries targeting government networks actively probe shadow IT applications because they are the weakest link in an otherwise hardened perimeter.
The Cybersecurity and Infrastructure Security Agency (CISA) has explicitly flagged the use of commercial messaging applications for government business as a risk factor in its guidance on securing government communications. The 2023 Microsoft Exchange breach, which compromised email accounts across multiple US government agencies, was enabled in part by credential exposure through third-party integrations that fell outside standard security monitoring.
Managing shadow IT: a framework for government IT leaders
Managing shadow IT in government requires more than policy enforcement. Banning unauthorized tools without providing credible alternatives guarantees continued workarounds. The effective approach combines discovery, governance, and substitution.
1. Discover what is actually in use
Most government IT departments underestimate the scope of shadow IT in their organization. Network traffic analysis, endpoint monitoring, and user surveys are the primary discovery mechanisms. Tools like Cloud Access Security Brokers (CASBs) can identify unsanctioned SaaS applications in use across an organization.
Shadow IT discovery should be treated as a continuous function, not a one-time audit. New tools enter the ecosystem constantly, and the threat landscape evolves with them. Organizational security posture requires ongoing visibility rather than periodic snapshots.
2. Classify and prioritize risk
Not all shadow IT carries equal risk. A team using an unapproved project management tool for internal scheduling poses different risks than a team using consumer messaging apps for operational communications. Risk classification should account for data sensitivity, jurisdictional exposure, and the criticality of the workflow.
Prioritize enforcement where the intersection of data sensitivity and platform risk is highest: encrypted communications, file sharing of classified or sensitive material, and any tool used in mission-critical communications workflows.
3 Replace, don't just restrict
The most durable solution to shadow IT is eliminating the gap that creates demand for it. If approved tools meet operational needs, the incentive to adopt unauthorized alternatives disappears. Government IT departments should evaluate approved platforms against the functional requirements that are driving shadow IT adoption — real-time collaboration, mobile access, cross-agency interoperability, and ease of use.
Sovereign, self-hosted communication platforms purpose-built for government use offer a direct path to eliminating the most dangerous category of shadow IT: unauthorized messaging. Secure government communication platforms can provide the functionality of consumer tools with the compliance controls, data sovereignty, and auditability that government environments require.
For European agencies specifically, the combination of GDPR exposure and NIS2 obligations makes the case for digital sovereignty in communications infrastructure particularly urgent. Microsoft Teams alternatives designed for European government have emerged precisely to address this gap, offering data residency within EU jurisdiction and auditability aligned with European regulatory requirements.
Sovereign communication platforms as a structural fix
The most direct response to shadow IT in government communications is deploying a platform that outcompetes consumer tools on usability while meeting institutional requirements on security, compliance, and sovereignty.
Self-hosted, open-source communication tools for government offer several structural advantages: full control over data residency, the ability to operate in air-gapped environments, and integration with existing identity and access management infrastructure. These are not features that consumer platforms offer, regardless of their enterprise tier.
For defense and intelligence contexts, the bar is higher still. Military communication requirements include end-to-end encryption at the infrastructure level, not just in transit, support for classified network environments, and fine-grained access controls that map to organizational hierarchy. Consumer platforms cannot satisfy these requirements. Military messaging platforms built for operational environments close this gap and, in doing so, remove the operational pressure that drives shadow IT adoption.
Government messaging applications purpose-built for public sector use also address the cross-agency interoperability problem. When agencies can communicate securely across organizational boundaries using approved infrastructure, the use of WhatsApp or Signal as an interoperability workaround becomes unnecessary.
Encrypted messaging at the infrastructure level gives government IT departments control over key management, audit logging, and data retention. A review of encrypted messaging apps reveals a significant gap between consumer-grade and government-grade implementations, particularly around key custody and metadata protection.
For European governments, a sovereign Slack alternative with EU data residency eliminates the jurisdictional exposure that US-headquartered platforms create. Secure messaging for European governments is now a distinct product category because the regulatory environment demands it.
Communication security in government is not a feature request. Platforms that treat it as an afterthought generate the conditions under which shadow IT flourishes. The most secure messaging apps for government use share a common architecture: end-to-end encryption, self-hosted deployment, open-source auditability, and compliance controls aligned with national and sector-specific regulatory frameworks. Government chat infrastructure built on these principles gives IT administrators the visibility and control that consumer platforms structurally cannot provide.
Frequently asked questions about <anything>
shadow IT in government
What is shadow IT in government?
Why is shadow IT so prevalent in government agencies?
What are the main risks of shadow IT in government?
How can government IT departments detect shadow IT?
What is the most effective way to manage shadow IT in government?
Does shadow IT in government create GDPR compliance risks?
What types of platforms eliminate the need for shadow IT in government communications?


- Digital sovereignty
- Federation capabilities
- Scalable and white-labeled


- Highly scalable and secure
- Full patient conversation history
- HIPAA-ready

for mission-critical operations
- On-premise and air-gapped ready
- Full control over sensitive data
- Secure cross-agency collaboration
%201.svg)

- Open source code
- Highly secure and scalable
- Unmatched flexibility


- End-to-end encryption
- Cloud or on-prem deployment
- Supports compliance with HIPAA, GDPR, FINRA, and more


- Supports compliance with HIPAA, GDPR, FINRA, and more
- Highly secure and flexible
- On-prem or cloud deployment



.avif)


