.png)
End-to-end encryption for government is now a directive, not a recommendation
For EU government organizations and critical infrastructure operators, end-to-end encryption is no longer an architectural choice — it is a regulatory obligation. NIS2, which came into force across EU member states in October 2024, explicitly requires essential and important entities to implement encryption as part of their cybersecurity risk management measures. GDPR Article 32 has required encryption of personal data since 2018. And in February 2024, the European Court of Human Rights delivered its landmark ruling in Podchasov v. Russia: weakening E2EE or mandating backdoors violates the human right to privacy under Article 8 of the European Convention on Human Rights.
The global threat landscape reinforces what EU law already mandates. In late 2024, Chinese state-affiliated threat actors compromised at least eight US telecommunications carriers in a campaign known as Salt Typhoon, intercepting calls and messages of government officials and their communications including senior political figures. US agencies CISA and FBI responded by directing officials to adopt E2EE immediately. The relevance for EU operators is direct: the same threat actor group has been active against European telecoms and public administration, and the attack techniques are identical.
The conclusion is the same on both sides of the Atlantic: unencrypted communications on commercial infrastructure cannot be considered safe for secure government team chat or any sensitive operational use. The difference is that in the EU, this is not just a security recommendation — it is a legal requirement with enforcement consequences.
Why state-level interception threats matter for EU infrastructure operators
The Salt Typhoon campaign is the clearest recent example of how nation-state actors exploit telecommunications infrastructure at scale. It was a broad cyber-espionage operation against critical infrastructure, executed by PRC state-sponsored actors, designed to achieve persistent, long-term access across multiple carrier networks simultaneously. The group is tracked under multiple names including RedMike, OPERATOR PANDA, and UNC5807, and has been active since at least August 2019.
What made this campaign operationally significant for EU decision-makers was not its US target — it was its method. The attackers exploited lawful intercept infrastructure: systems designed to allow authorized access to communications. When those access points exist, they become targets. The EU's regulatory rejection of backdoors is not ideological; it reflects this operational reality. Any system built to allow interception under legal authorization is also exploitable by adversaries who gain access to that mechanism.
Virtru CEO John Ackerly observed: "A system vulnerable to lawful interception is also vulnerable to unlawful intrusion."
For EU defense and critical infrastructure operators, the implication is structural: E2EE eliminates this category of vulnerability entirely by ensuring that intercepted data cannot be read even if the transmission infrastructure is compromised. Organizations operating in sensitive environments are increasingly evaluating air-gapped collaboration for government as the highest-assurance deployment model.
The scope of PRC targeting extends directly into European networks. ENISA's threat landscape reports confirm that state-affiliated actors are targeting EU telecoms, public administration, transport, and energy infrastructure using the same persistent access techniques observed in the US campaigns. The case for self-hosted chat for government has strengthened considerably in this context, removing reliance on third-party cloud infrastructure that remains exposed at the carrier level.
The backdoor debate has a definitive answer
The EU has resolved the policy argument over encryption backdoors more decisively than any other jurisdiction. On 13 February 2024, the European Court of Human Rights ruled in Podchasov v. Russia that weakening end-to-end encryption or creating backdoors infringes the human right to privacy under Article 8 of the ECHR. The court found that legislation requiring decryption access leads to general and indiscriminate surveillance and cannot be justified as a proportionate measure. This ruling is binding in its implications for all 46 member states of the Council of Europe.
The ECHR ruling came alongside the European Court of Human Rights ruled on the case — and it aligned precisely with what the Salt Typhoon incident demonstrated empirically: when a system can be decrypted by one party on demand, it can be compromised by any adversary with sufficient capability to access that mechanism. The US experience with CALEA — where lawful intercept infrastructure became the entry vector for a foreign intelligence operation — provides the operational evidence to support what the ECHR established in law.
The contrast with jurisdictions outside the EU is instructive. The UK's Online Safety Act contains provisions that could compel companies to weaken encryption. Apple withdrew iCloud E2EE from the United Kingdom rather than comply with a government backdoor request. UK government and defense users consequently lose access to the highest-grade commercial encryption available to EU peers. European governments are building frameworks around digital sovereignty for public institutions precisely to avoid this outcome and to maintain control over their communications infrastructure independently of policy decisions made in non-EU jurisdictions.
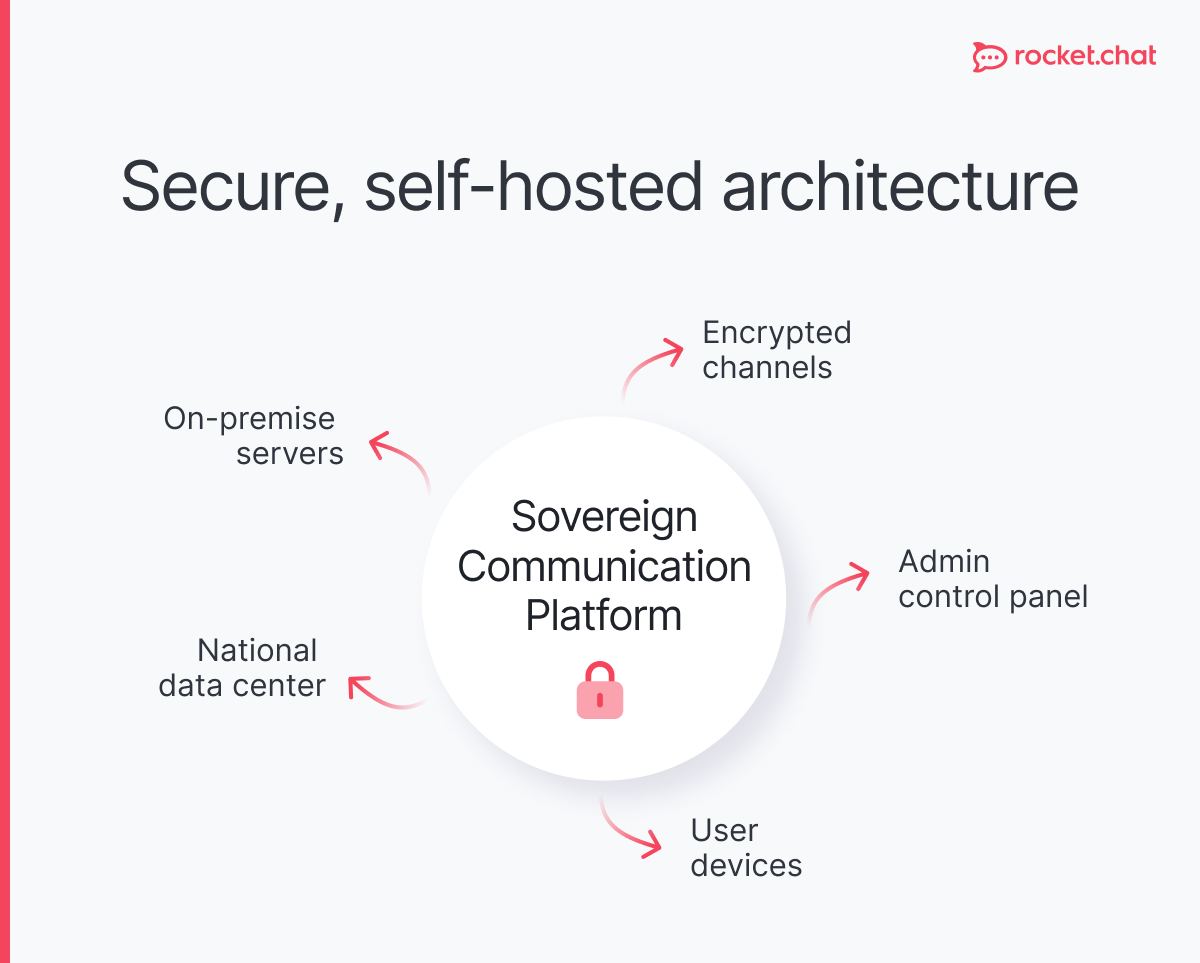
For EU organizations operating across multiple jurisdictions, the principle is clear: the EU framework is the most protective, and sovereign deployment models are the most defensible. The practical architecture for secure messaging for European governments increasingly involves on-premise or EU-hosted deployments that keep data and key management entirely within jurisdictions where E2EE is legally protected rather than threatened.
Post-quantum cryptography: the migration that cannot be deferred
NIST finalized its post-quantum cryptography standards in 2024, selecting CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures. ENISA has separately identified post-quantum cryptography as a critical priority for EU operators, noting that the transition must begin now given the long deployment cycles of government and critical infrastructure systems.
Harvest now, decrypt later is the most time-sensitive risk for classified and sensitive EU government data. State-affiliated adversaries with access to encrypted communications are storing that material today. When sufficiently powerful quantum computers become available, they will retroactively decrypt it. Data with a long sensitivity window — including diplomatic communications, personnel records, infrastructure specifications, and procurement data — is already at risk from material collected today. Compliance frameworks such as NIS2 compliance for critical infrastructure are beginning to incorporate PQC readiness as an explicit requirement for operators across EU member states.
The encryption software market, valued at $14.5B in 2023, is projected to reach $60.7B by 2033 at a compound annual growth rate of 15.4%. EU government and critical infrastructure sectors are significant drivers of that growth, reflecting both NIS2 compliance investment and the scale of PQC migration ahead.
The practical implication for EU government and critical infrastructure operators: procurement and deployment cycles for encryption infrastructure run in years, not weeks. Beginning PQC audits now, mapping current TLS and key management infrastructure, and building migration roadmaps is not a future project. Adversaries are collecting ciphertext today with the intent to decrypt it when quantum capability is available. For organizations subject to data protection regulation, GDPR-compliant messaging for government platforms must also account for PQC readiness in their vendor assessments.

The EU regulatory position: aligned, not contradictory
The EU stands apart from other major jurisdictions in having a consistent, coherent regulatory position on E2EE: it is required, and mandated backdoors are incompatible with fundamental rights. NIS2 requires encryption as a risk management measure. GDPR Article 32 requires it for personal data protection. The ECHR ruling prohibits legislation that undermines it. ENISA recommends it operationally. These frameworks are mutually reinforcing, not in conflict.
This coherence has direct consequences for procurement and platform selection. EU government organizations and critical infrastructure operators evaluating Microsoft Teams alternatives for European government must assess whether a platform's encryption architecture, data residency, and key management model are compatible with NIS2, GDPR, and the sovereignty requirements increasingly embedded in public sector procurement rules across member states.
The contrast with the US regulatory environment is instructive, not directly applicable. In the US, the SEC and DOJ have pursued enforcement against use of encrypted messaging in regulated industries, while national security agencies simultaneously mandate E2EE. That contradiction creates genuine compliance risk for US-based organizations. EU organizations do not face the same internal conflict — but those operating transatlantic operations or using US-based platforms need to understand that the US posture does not reflect EU law, and should not drive EU procurement decisions.
For EU organizations, the resolution is architectural. A sovereign Slack alternative for Europe that supports E2EE with EU-based key management and auditable message retention satisfies NIS2, GDPR, and operational security requirements simultaneously. The architecture question is not whether to encrypt — EU law answers that — but how to implement encryption in a way that meets all applicable obligations without creating new dependencies on non-EU infrastructure.
Encryption across the threat spectrum: a comparison
Frequently asked questions about <anything>
end-to-end encryption for government
What is end-to-end encryption for government, and why does it matter for EU organizations?
What EU regulations require end-to-end encryption for government and critical infrastructure?
What is the difference between end-to-end encryption and transport encryption?
What does post-quantum cryptography mean for existing EU government encryption deployments?
Does the EU support encryption backdoors for law enforcement purposes?
How does NIS2 affect encryption requirements for EU government and critical infrastructure?
What are the limits of end-to-end encryption for EU government security?


- Digital sovereignty
- Federation capabilities
- Scalable and white-labeled


- Highly scalable and secure
- Full patient conversation history
- HIPAA-ready

for mission-critical operations
- On-premise and air-gapped ready
- Full control over sensitive data
- Secure cross-agency collaboration
%201.svg)

- Open source code
- Highly secure and scalable
- Unmatched flexibility


- End-to-end encryption
- Cloud or on-prem deployment
- Supports compliance with HIPAA, GDPR, FINRA, and more


- Supports compliance with HIPAA, GDPR, FINRA, and more
- Highly secure and flexible
- On-prem or cloud deployment



.avif)


